Workshop Title:
Detecting Botnets Using Machine Learning
Date:
May 15th, 2024 (GMT+1)
Organizer:
University of Oxford, UK
Keywords:
- Cybersecurity
- Machine learning
- Bots
- Botnets
- Hacking
- Spamming
Workshop Chair:
Personal Bio:
Dr Stavros Shiaeles is a Reader in Cyber Security at University of Oxford, UK, Visiting Prof. at University of Peloponnese, Greece and Bharath University, India. He worked as an expert in cyber-security and digital forensics in the UK and EU, serving companies and research councils. His research interests span in the broad area of Cyber Security such as OSINT, Social Engineering, Distributed Denial of Service Attacks, Cloud Security, Insider Threats, Digital Forensics, Network Anomaly Detection and Malware mitigation.
He authored more than 100 publications in academic journals and conference, he chaired many workshops in IEEE well-known conference such as IEEE Service and NetSoft, he is a member of IEEE TCIIN Group and IEEE TCHS and currently he is co-chairing IEEE International Conference on Security and Resilience Series (IEEE CSR). He has co-edited two Cyber Security books, published by CRC Press on April 2021 and he is involving as Principal Investigator, leading University of Oxford research team, in European and local grants.
Further to his academic qualifications, he holds a series of professional certifications named EC-Council Certified Ethical Hacker (CEH), EC-Council Advance Penetration Testing (CAST611), ISACA Cobit 5 Foundation and a Cyberoam(Now acquired by Sophos) Certified Network and Security Professional (CCNSP), and he is an EC-Council accredited instructor providing professional certifications training on Cybersecurity and Penetration testing.
It is worth mentioning, prior entering academia, he was in the industry, in which he has more than 10 years of experience, and he worked on various IT aspects and Cybersecurity.
Workshop Committee Members:
Dr. Bendiab Gueltoum Université Frères, Mentouri Constantine 1 (UFMC1) bendiab.kelthoum@umc.edu.dz
Dr. Oluwatobi Fajana, University of Oxford oluwatobi.fajana@port.ac.uk
Dr. Marwan Omar, Illinois Institute of Technology momar3@iit.edu
Workshop Description:
Background:
Botnets pose a significant problem in today's digital landscape. These networks of compromised computers, controlled by a central command, can wreak havoc on individuals, organizations, and even entire industries. Botnets are used for various malicious activities, including distributed denial-of-service (DDoS) attacks, spamming, credential theft, and data exfiltration. Their large-scale and coordinated nature make them difficult to detect and mitigate. Moreover, the increasing sophistication of botnet technologies makes them capable of evading traditional security measures. Combating botnets requires a multi-faceted approach, involving proactive monitoring, network segmentation, strong authentication mechanisms, and up-to-date security patches. Collaboration between cybersecurity experts, law enforcement agencies, and Internet service providers is crucial to effectively address the botnet problem and protect the integrity and privacy of our interconnected systems.
Goal/Rationale:
Botnet research faces numerous challenges that demand attention to effectively combat this pervasive cyber threat. One critical issue is the evolving sophistication of botnet technologies, making them adept at evading traditional detection mechanisms. To address this, researchers need to constantly analyze and understand emerging botnet tactics, techniques, and procedures (TTPs) to develop robust countermeasures. This requires active collaboration between academia, industry, and law enforcement agencies to share threat intelligence and stay ahead of the botnet landscape.
Another research challenge is the scalability of botnet detection and mitigation techniques. As botnets grow in size and complexity, the sheer volume of network traffic and data poses significant computational and processing challenges. Researchers must explore scalable approaches such as distributed detection mechanisms, parallel processing, and intelligent data analysis to handle the vast amounts of data generated by botnets.
Additionally, the ability to accurately attribute and identify botnet operators remains a significant research problem. Improved attribution techniques, combined with legal frameworks and international cooperation, are essential for effectively prosecuting botnet operators and disrupting their infrastructure.
Lastly, mitigating the collateral damage caused by botnets is crucial. Research should focus on developing techniques to minimize the impact on innocent users and compromised systems while effectively neutralizing botnets.
By addressing these research issues and promoting interdisciplinary collaboration, we can enhance our understanding of botnets and develop more effective strategies to detect, mitigate, and dismantle these harmful networks.
Scope and Information for participants
The scope of the workshop on Botnets is to provide attendees with a comprehensive understanding of how botnets works and how machine learning could help to identify them. The workshop covers a wide range of topics, including:
- Various Botnets
- Machine learning algorithms used for detection
- Features for detection
- Python Libraries available
The workshop is designed to be comprehensive, covering all aspects of botnet detection and is suitable for anyone wants to learn more about Botnets and how to identify them.
Highlights
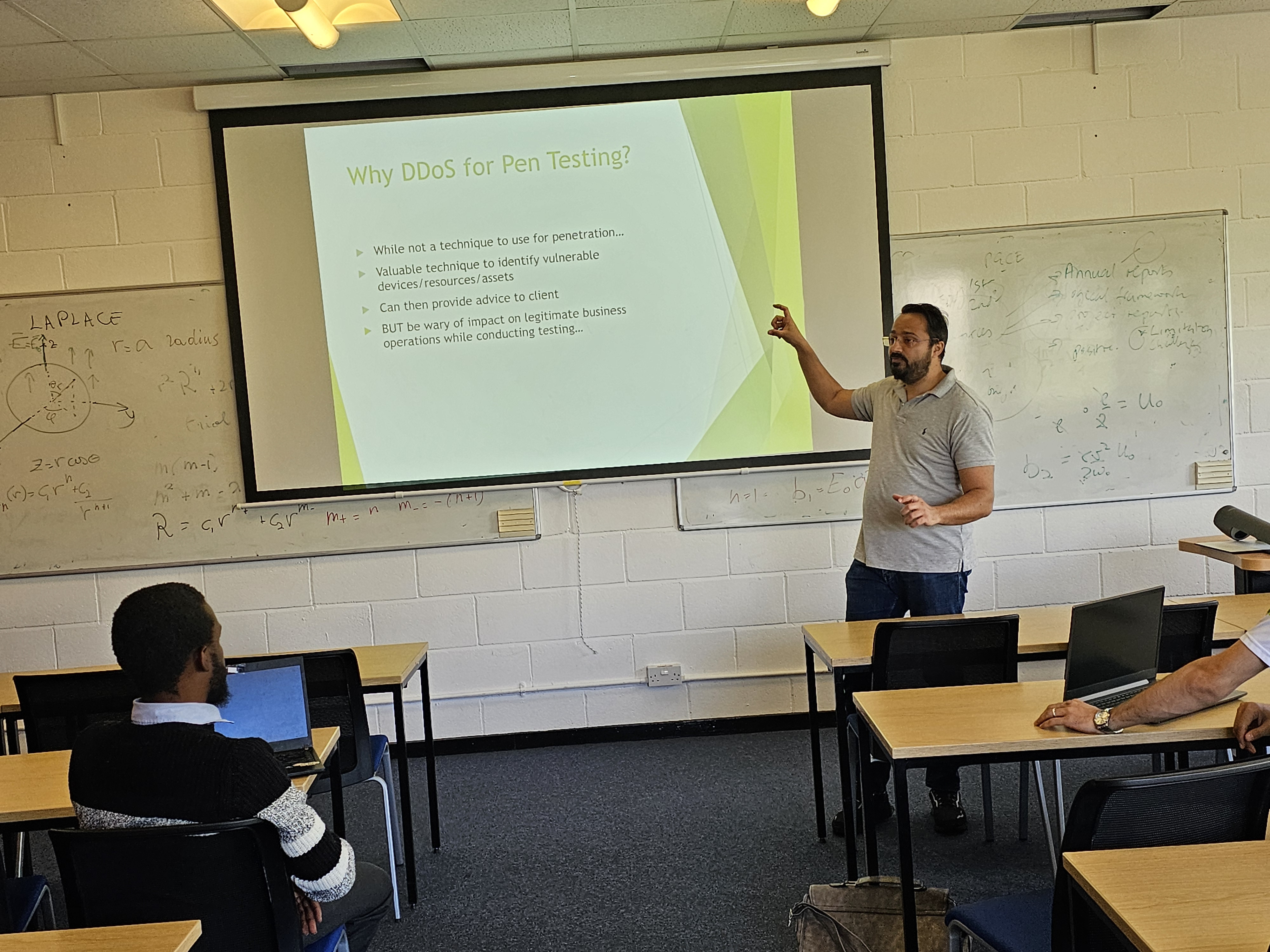
On July 2, 2025, the University of Oxford hosted an insightful workshop focused on using machine learning techniques to detect botnets. The session, aimed at cybersecurity professionals and students, explored advanced methods for identifying botnet activities within network traffic. The workshop began with an overview of botnets and their evolving threat landscape. Participants then delved into various machine learning algorithms, including supervised and unsupervised learning, used for botnet detection. Practical sessions demonstrated data preprocessing, feature extraction, and model training using real-world datasets. Attendees also learned about evaluating model performance and the importance of continuous learning to adapt to new botnet strategies. The workshop emphasized the need for robust data collection and the ethical implications of using machine learning in cybersecurity. Interactive discussions and Q&A sessions provided deeper insights, enabling participants to apply these techniques in their professional environments. The event underscored the critical role of machine learning in enhancing cybersecurity measures against botnet threats.



Venue:
Buckingham Building, University of Oxford, Oxford PO1 3HE, UK
VISA
Welcome to GOV.UK (www.gov.uk)In order to ensure the information is correct and up to date, there may be changes which we are not aware of. And different countries have different rules for the visa application. It is always a good idea to check the latest regulations in your country. This page just gives some general information of the visa application.
UK Visa Information
What you need to do
- Check if what you plan to do in the UK is allowed as a Standard Visitor.
- Check you meet the eligibility requirements.
- Check if you need to apply for a visa to visit the UK.
- Apply for a Standard Visitor visa online - if you need one.
Check you meet the eligibility requirements
You must have a passport or travel document to enter the UK. It should be valid for the whole of your stay.
You must be able to show that:
- you'll leave the UK at the end of your visit
- you're able to support yourself and your dependants during your trip (or have funding from someone else to support you)
- you're able to pay for your return or onward journey (or have funding from someone else to pay for the journey)
- you'll not live in the UK for extended periods through frequent or successive visits, or make the UK your main home
Check if you need a visa to visit the UK
Depending on your nationality, you'll either:
- have to apply for a Standard Visitor visa before you travel to the UK
- be able to visit the UK for up to 6 months without needing a visa
You can check if you need a visa before you apply.
If you do not need a visa, you must still meet the Standard Visitor eligibility requirements
to visit the UK.
You may be asked questions at the UK border about your eligibility and the activities you
plan to do.
Attend in person:
If you want to attend the workshop on-site, please email the Conference Committee: info@confseml.org.
